Command Palette
Search for a command to run...
ClawKeeper : Protection de sécurité complète pour les agents OpenClaw grâce aux Skills, Plugins et Watchers
ClawKeeper : Protection de sécurité complète pour les agents OpenClaw grâce aux Skills, Plugins et Watchers
Résumé
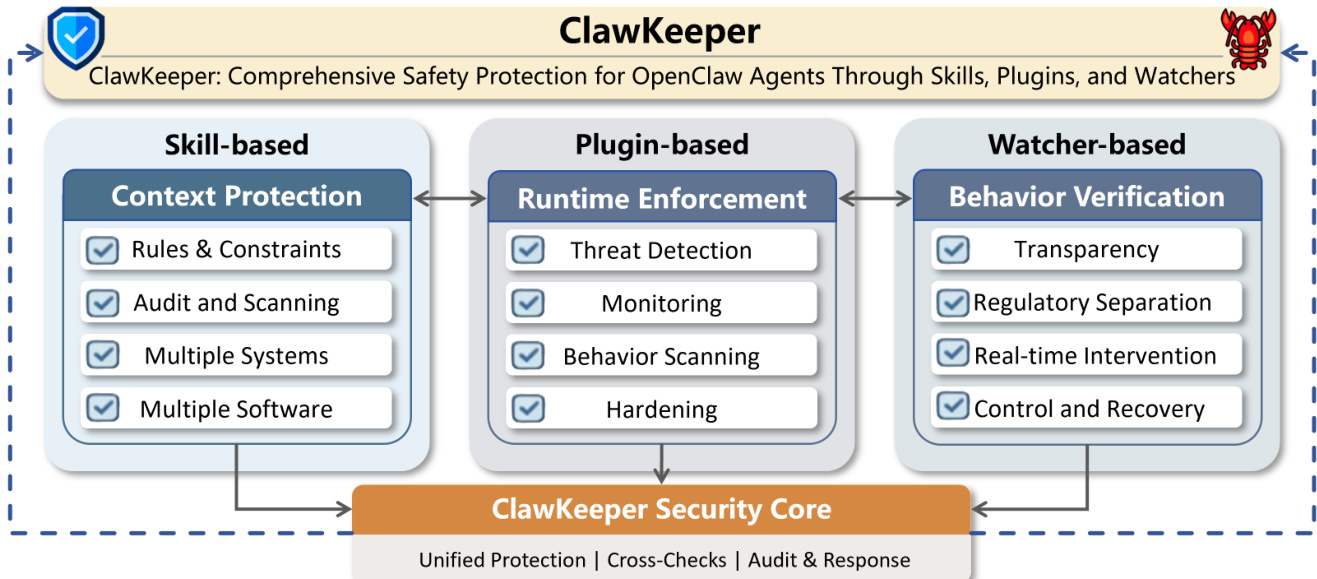
OpenClaw s'est rapidement imposé comme un environnement d'exécution (runtime) d'agents autonomes open source de premier plan, offrant des fonctionnalités puissantes telles que l'intégration d'outils, l'accès aux fichiers locaux et l'exécution de commandes shell. Toutefois, ces privilèges opérationnels étendus introduisent des vulnérabilités de sécurité critiques, transformant les erreurs de modèle en menaces tangibles au niveau du système, notamment la fuite de données sensibles, l'élévation de privilèges et l'exécution de compétences tierces malveillantes. Les mesures de sécurité existantes au sein de l'écosystème OpenClaw restent hautement fragmentées, ne traitant que des étapes isolées du cycle de vie de l'agent plutôt que de fournir une protection holistique. Pour combler cette lacune, nous présentons ClawKeeper, un cadre de sécurité en temps réel intégrant des mécanismes de protection multidimensionnels à travers trois couches architecturales complémentaires. (1) La protection basée sur les compétences (Skill-based protection) opère au niveau des instructions en injectant des politiques de sécurité structurées directement dans le contexte de l'agent, afin d'imposer des contraintes spécifiques à l'environnement et de respecter les frontières interplateformes. (2) La protection basée sur les plugins (Plugin-based protection) agit comme un exécuteur interne du runtime, offrant un renforcement de la configuration, une détection proactive des menaces et une surveillance continue du comportement tout au long du pipeline d'exécution. (3) La protection basée sur le surveillant (Watcher-based protection) introduit un middleware de sécurité au niveau du système, novateur et découplé, qui vérifie en continu l'évolution de l'état de l'agent. Elle permet une intervention en temps réel sur l'exécution sans être couplée à la logique interne de l'agent, en supportant des opérations telles que l'arrêt d'actions à haut risque ou l'imposition d'une confirmation humaine. Nous soutenons que ce paradigme du surveillant (Watcher) présente un fort potentiel pour servir de brique fondamentale dans la sécurisation des systèmes d'agents autonomes de nouvelle génération. Des évaluations qualitatives et quantitatives extensives démontrent l'efficacité et la robustesse de ClawKeeper face à divers scénarios de menaces. Notre code est mis à disposition.
One-sentence Summary
Researchers from Beijing University of Posts and Telecommunications and the Beijing Academy of Artificial Intelligence propose ClawKeeper, a unified security framework for OpenClaw agents that integrates skills, plugins, and a novel decoupled Watcher to enable real-time, adaptive defense against system-level threats while resolving the safety-utility tradeoff.
Key Contributions
- The paper introduces ClawKeeper, a real-time security framework that integrates multi-dimensional protection across three architectural layers to address fragmented safety measures in the OpenClaw ecosystem. This unified approach combines instruction-level policy injection, runtime enforcement, and decoupled system monitoring to provide holistic coverage throughout the agent lifecycle.
- A novel Watcher-based protection mechanism is presented as a standalone external middleware that verifies agent state evolution and enables real-time intervention without coupling to internal logic. This design separates safety oversight from task execution, allowing the system to halt high-risk actions or enforce human confirmation while avoiding the traditional safety-utility tradeoff.
- Extensive qualitative and quantitative evaluations demonstrate the effectiveness and robustness of the framework across diverse threat scenarios, including sensitive data leakage and malicious skill execution. The work validates that this three-layer architecture outperforms existing point defenses by adapting to emerging threats and providing continuous behavioral monitoring.
Introduction
As autonomous Agents like OpenClaw evolve into operating system-like environments with direct access to local files and shell commands, they introduce critical security risks where model errors can escalate into system-level threats such as data leakage and privilege abuse. Prior security measures suffer from fragmented coverage that addresses only isolated lifecycle stages, while also struggling with a safety-utility tradeoff, reactive post-hoc analysis, and static defense mechanisms that cannot adapt to the agent's self-evolving nature. To address these gaps, the authors present ClawKeeper, a unified real-time security framework that integrates multi-dimensional protection across three layers: instruction-level Skill policies, runtime Plugin enforcement, and a novel decoupled Watcher middleware that enables proactive intervention and regulatory separation without coupling to the agent's internal logic.
Dataset
- The authors construct a benchmark to assess the security capabilities of CLAWKEEPER, comprising seven safety task categories aligned with the OWASP Agent Security Initiative and open-source defense taxonomies.
- Each of the seven categories contains 20 adversarial instances, split equally into 10 simple and 10 complex examples.
- Human annotators independently score every instance to determine if the defense succeeds, following the evaluation protocol of AgentSafetyBench.
- The dataset serves as a systematic evaluation tool rather than a training corpus, with no specific training splits or mixture ratios mentioned for model development.
- Representative examples and definitions for each category are summarized in Table 4 of the paper.
Method
The authors propose ClawKeeper, a comprehensive security framework designed to unify three complementary protection paradigms into a multi-layered architecture for the OpenClaw ecosystem. This system integrates skill-based context enforcement, plugin-based runtime hardening, and an independent Watcher for external behavior verification. Refer to the framework diagram for a high-level view of how these three pillars converge into a unified security core.
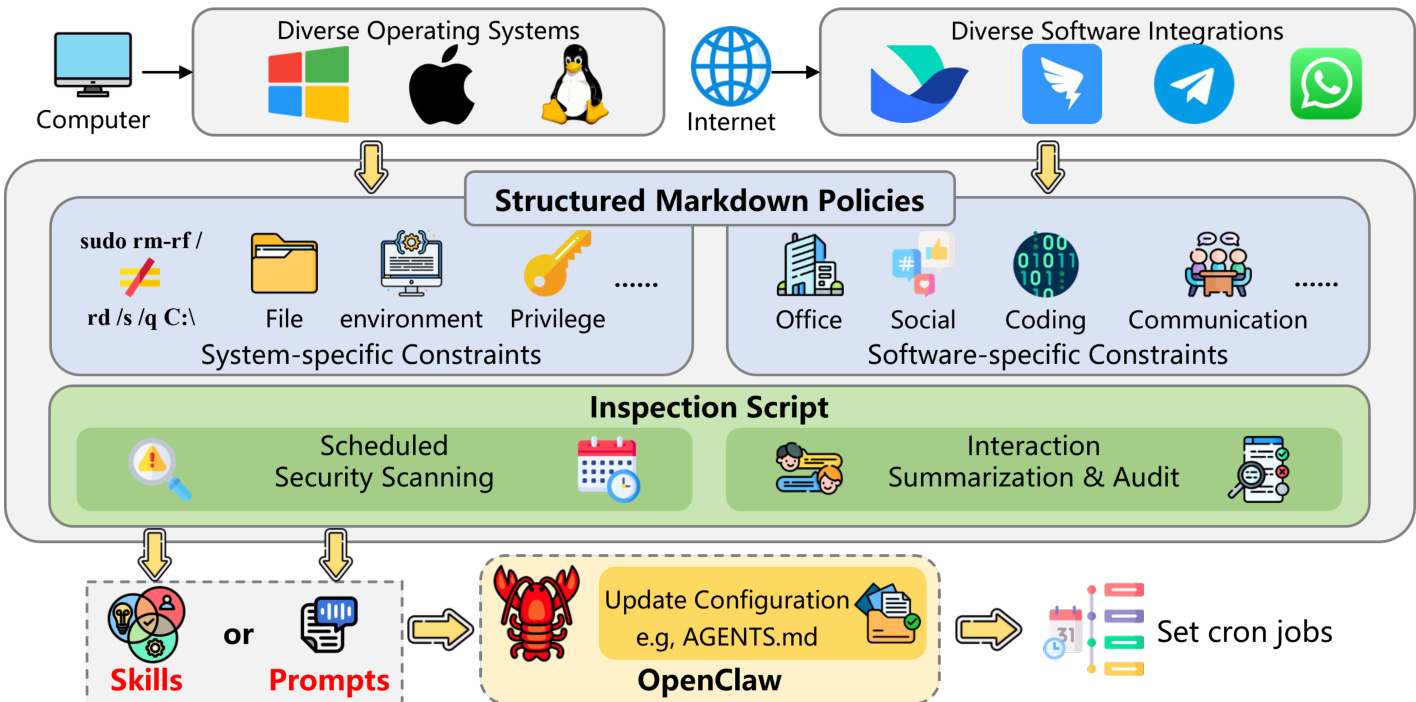
The first layer, Skill-based Protection, operates at the instruction level where the agent constructs its inference context. Security rules are defined as structured Markdown documents that the agent can directly interpret and enforce. This design allows for low-cost deployment without modifying the underlying framework. The protection mechanism covers two dimensions: system-level constraints for diverse operating systems like Windows and Linux, and software-level constraints for communication platforms such as Telegram or Feishu. To enhance robustness, the framework incorporates inspection scripts that perform scheduled security scanning and interaction summarization. As shown in the figure below, this approach allows policies to be continuously applied throughout the entire interaction lifecycle.
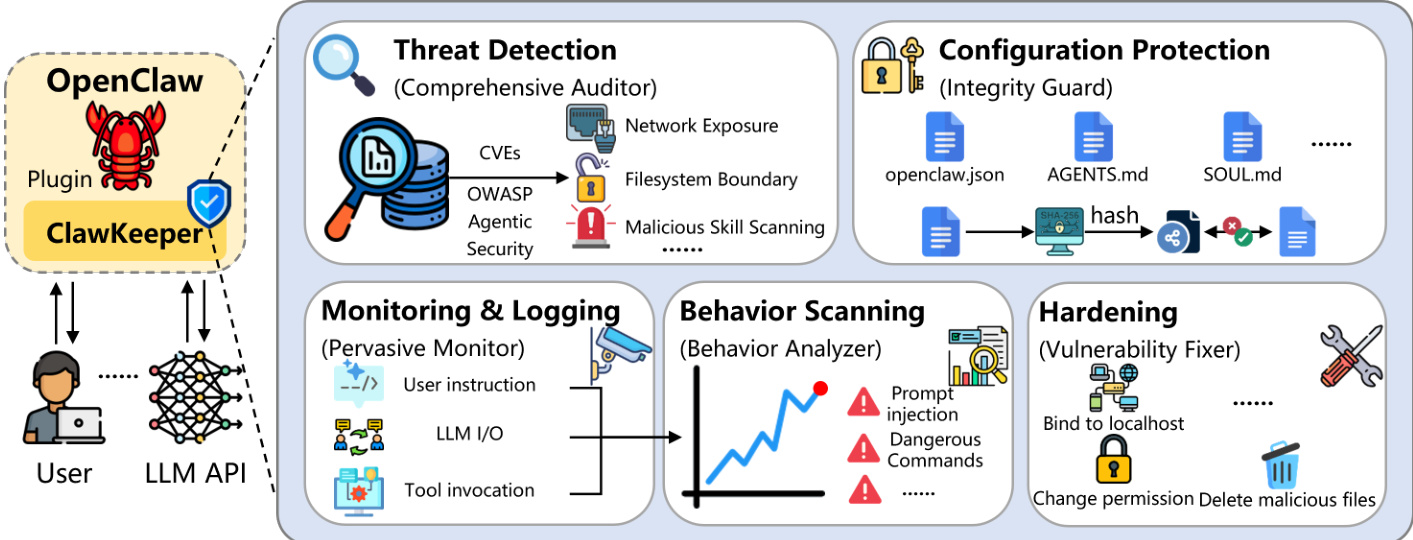
The second layer, Plugin-based Protection, functions as a hard-coded enforcement layer within the OpenClaw runtime. Unlike prompt-level defenses, this module affords direct control over system behavior to ensure comprehensive security coverage. The plugin acts as a comprehensive security auditor, scanner, and hardening enforcer. It executes detailed Threat Detection to identify misconfigurations and known vulnerabilities aligned with OWASP Agentic Security guidelines. To maintain integrity, the Configuration Protection module generates cryptographic hash backups of critical operational files. Furthermore, a Behavior Scanning mechanism analyzes historical execution flows to detect latent threat patterns such as prompt injections or dangerous commands. The figure below illustrates the specific modules including Threat Detection, Configuration Protection, Monitoring, Behavior Scanning, and Hardening.
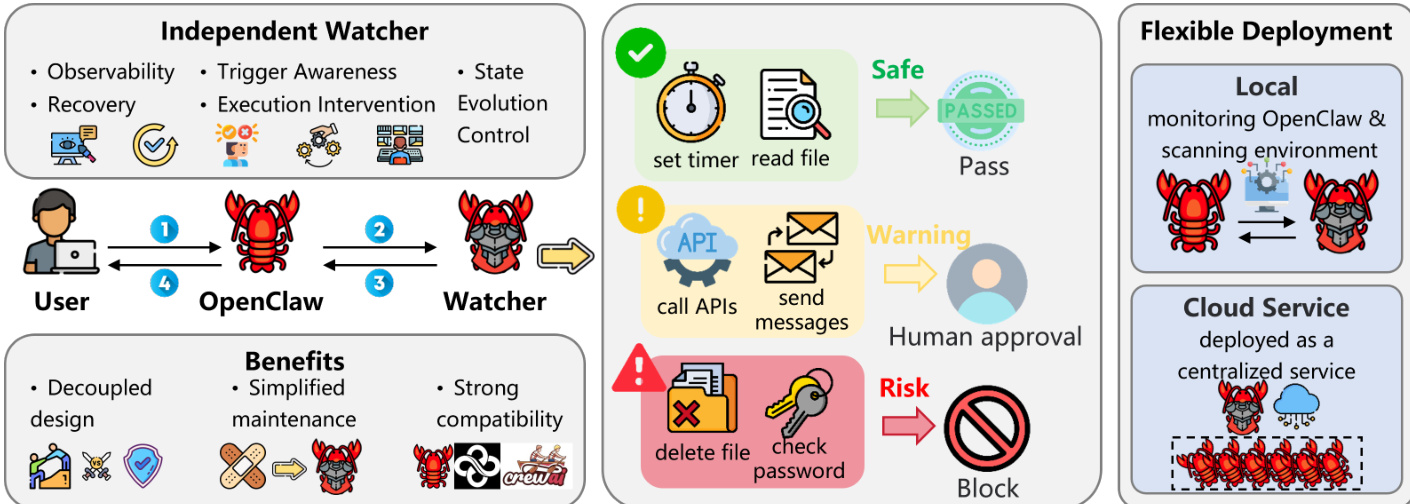
The third layer, Watcher-based Protection, introduces an independent external agent that functions as a dedicated security auditor. This decoupled architecture addresses the limitations of tightly coupled safety components by separating task execution from safety enforcement. The Watcher is implemented as a separate OpenClaw instance equipped with specialized monitoring skills. It communicates with the task-executing agent via a persistent WebSocket connection to perform real-time safety diagnosis. If a potentially unsafe trajectory is detected, the Watcher signals the agent to pause and seek user confirmation. The framework supports flexible deployment configurations, including Local Deployment for privacy-sensitive scenarios and Cloud Deployment for centralized governance. As shown in the figure below, the Watcher provides observability, trigger awareness, and execution intervention while maintaining a decoupled design.
Experiment
- Comparative evaluation against seven open-source baselines validates that CLAWKEEPER's unified three-layer architecture achieves significantly higher defense success rates across all seven safety task categories, whereas existing methods suffer from severe coverage fragmentation and only moderate effectiveness within their limited scopes.
- Self-evolution experiments demonstrate that the Watcher component continuously improves its defense capabilities by processing new adversarial cases, increasing success rates through dynamic updates to monitoring skills and risk thresholds, a capability absent in static plugin or skill-based approaches.
- Qualitative case studies confirm that skill-based protection effectively enforces context-aware security protocols at system and software perimeters while enabling autonomous periodic self-auditing without human intervention.
- Plugin-based assessments validate that the Hardening module prevents sensitive data exfiltration by injecting risk-aware rules into core configurations, while integrated scanners successfully identify latent vulnerabilities and provide actionable remediation steps.
- Watcher-based scenarios illustrate the system's ability to intercept unsafe behaviors in real-time, including blocking dangerous command execution, halting excessive tool chaining, and stopping automated retry loops following upstream failures to enforce strict human-in-the-loop safety policies.